Cyber-attacks are a big threat and happen all the time these days. Hackers try to steal important information or money from businesses by hacking their computers and networks. If they attack your business, it can mean bad news, and you might have to close while fixing damage temporarily. The good news is there are key steps you can take to lock down security and prevent most attacks from succeeding in the first place. Doing things like using strong passwords, training employees on safe internet use, keeping software updated, monitoring for threats, and having a response plan can stop over 80% of attacks.
In this article will discuss the best ways to protect businesses from cyber-attacks.
What is Cyber Attack?
Cyber-attacks happen when someone tries to hack into your computers or networks to steal stuff, spy, cause damage, or make money. They’re companies, criminals, hackers, and even foreign governments trying to steal private information like passwords, financial data, or social security numbers. The hackers write harmful software to break system security or trick someone into sharing personal information. They can also lock up company data for ransom until you pay.
Over 60% of small businesses say they’ve been hacked somehow. More and more cyber-attacks happen every day, costing companies a lot when important information gets stolen. Victims must shut down temporarily to fix damage, notify customers, and deal with accounting messes.
9 Ways to Protect Your Business from Cyber Attack
Looking for some tips and ways to protect your business against cyber-attacks? Here are the nine best and easiest ways to protect your business from cyber-attacks and hackers.
9 Ways to Protect Your Business from Cyber Attack
Looking for some tips and ways to protect your business against cyber-attacks? Here are the nine best and easiest ways to protect your business from cyber-attacks and hackers.
9. Use Antivirus and Anti-Malware Tools
Having antivirus or anti-malware tools set up is a must. Over 30% of cyber-attacks involve harmful software. Choose a good, paid anti-malware company that updates itself automatically to catch the latest bugs and problems. Ensure every laptop, computer, phone, and tablet has this protection software before connecting to company systems and wifi. It creates a major shield to stop attacks from getting through.
Even employees working remotely need their home devices protected. Antivirus scans files and blocks cyber threats if they detect anything dangerous in emails, downloads, or website pop-ups someone clicks. It’s one of the best defenses. Without it, attacks can spread fast once in our network.
8. Keep Your Software and Security Up-To-Date
Outdated programs and apps have weaknesses. Set all employee devices, operating systems, and antivirus tools to update themselves whenever new fixes and patches come out, about every 2 weeks. This seals up security holes that hackers try to exploit.
It only takes a quick second for computers and phones to install the latest upgrades that could stop an attack automatically. Don’t hit snooze or postpone updates when they pop up. Keeping everything fresh means hackers have a way harder time finding a way into systems
Human mistakes lead to over 90% of successful cyber-attacks. We have to regularly show employees how to spot suspicious links in emails, unsafe attachments someone sends, and phishing scams asking for money or login details, and drill into them how to create long, strong passwords. Train everyone on how hackers try to fool or trick them online.
Education does reduce company risk more than anything else we can do technology-wise. Employees are the first line of defense for security. Give them the tools and knowledge so they don’t accidentally click, download, or share something harmful even when it looks friendly, official, or work-related.
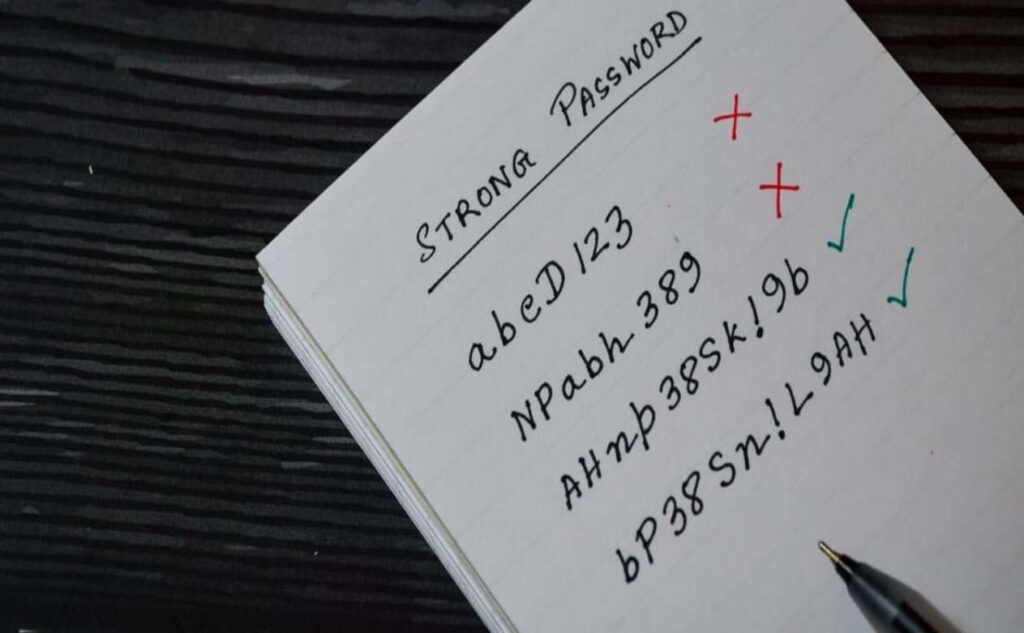
6. Have Strong Password Policies
Ensure that all employees use long passwords with capital and lowercase letters, special characters, even emojis, the more random the better. Under 12 characters are too weak. Change passwords every 60-90 days, too, so hackers can’t use old ones they steal. Make everyone set up optional multi-factor login as well, needing a code texted when logging into stuff for extra security.
Over 80% of hacking starts with guessing weak or reused passwords, so locking them down makes life harder for attackers. Also, control who has network, computer, and database access based on their job at the company and actual needs. Follow the password basics for better protection.
5. Backup and Encrypt Sensitive Data
Always make encrypted copies of sensitive company files and customer details on physical drives kept here and backed up at a secure cloud storage provider off-site. Use tough data encryption from start to finish with long passphrases, too, meaning even if a backup hard drive walks away or a cloud account gets hacked, info is useless to attackers without the encryption key to unlock it.
4. Monitor Activity and Networks
Use firewall security tools, threat monitoring, and data analytics 24/7 to sniff out shady network traffic, unauthorized login attempts from sketchy places, vulnerabilities like outdated software, and suspicious activity. The early warning means we can shut down an attack before major harm or data theft occurs. Over 60% of companies surveyed say near-instant analytics and threat detection have prevented cyber-attack damage for them before it was too late.
4. Monitor Activity and Networks
Use firewall security tools, threat monitoring, and data analytics 24/7 to sniff out shady network traffic, unauthorized login attempts from sketchy places, vulnerabilities like outdated software, and suspicious activity. The early warning means we can shut down an attack before major harm or data theft occurs. Over 60% of companies surveyed say near-instant analytics and threat detection have prevented cyber-attack damage for them before it was too late.

3. Control Access with Firewalls and Authentication
Firewalls block suspicious traffic, emails, and hacker IPs trying to sneak into company networks where they don’t belong. A multi-factor login, needing a code sent to employee phones, also helps keep out anyone without approval. Maintain walls between public web networks guests use, employee WiFi and systems, business databases with key files, and other sensitive data to limit exposure. Over 70% of businesses surveyed say tight access controls have prevented unauthorized users from accessing private systems and data.
2. Have an Incident Response Plan Ready
It’s a matter of when, not if, a cyber-attack or data breach will happen these days. Over 60% of small businesses suffered a successful cyber-attack last year. However, having an incident response plan makes all the difference in recovery time and getting back up and running.
Outline necessary steps like immediately checking systems for compromise, isolating affected parts that got hacked, securely restoring recent accessible data backups, notifying customers and authorities as legally needed, investigating entry points, boosting security holes, and practicing simulated threat scenarios.
1. Get Cyber Insurance
If disaster somehow strikes despite security efforts, having specialty cyber insurance can be vital to continued operations. It can cover costs related to the investigation of the attack, income lost from downtime or operations halt, lawsuits from affected customers, overall repair damages, forensic analysis to ID the attackers, crisis management PR, and more, things that quickly add up after a breach.
Over 75% of cyber insurance claim payouts were over $100k last year. Locking down our defenses first is key, but insurance ensures the business survives. Having a plan with a knowledgeable insurer also forces you to meet security compliance standards.

Conclusion:
Protecting your company from cyber-attacks and online threats isn’t as hard as it may seem. By implementing good digital security habits like using strong passwords, training staff, keeping software patched and updated, monitoring activity, controlling access, securing backups, and having an incident response plan, you can lock things down and prevent over 85% of common attacks.
No organization is hack-proof, but staying vigilant, verifying security tools are working, testing defenses with audits, and following cyber security best practices make a breach far less likely, and limit damage if it somehow occurs.
Contact us today and get answers to all your queries from our experts, who will provide you with the best advice you need to protect your business against cyber-attacks!





